How To Find SQL Injection Vulnerabilities Automatically
There are many way finding SQL Injection Vulnerabilities manually. But, in this article, I will show you how to find SQL Injection Vulnerabilities automatically. It’s no different than finding it manually. The process mainly involves three tasks :
- Identifying Data Entry.
- Inject Data to Database.
- And last, detect anomalies from it’s response
In this part, you will see that you can do it automatically to a certain process. Identifying data entry (1st step) is something that can be automated. You can do it by just crawl the website and finding GET and POST request. As well ass Data Injection (2nd step), can also be done in an automatic fashion. The main problem is the 3rd step ( Detect Anomalies Response of Remote Server ). Although this part is easy for human to detect. it sometimes very difficult for a bot or software to detect it and fully understand output of the remote server. For example, when the web application returns the SQL error from database or when the web application returns HTTP 500 code error.
On the other hand, Bot program are systematic and through. They do not understand the logic of web application. But they have upper hand when testing a lot of potential vulnerabilities SQL injection.
Software For Automatically Find SQL Injection Vulnerabilities
There are many tools/software for Automatically Finding SQL Injection Vulnerabilities. One of them is HP WebInspect. WebInspect is a commercial tool created by Hewlett-Packard. It can also be used to find SQL Injection Vulnerabilities. However, the main purpose of this software is to conduct a full assessment of website’s security. Web Inspect is easy to use and requires no technical knowledge.
WebInspect
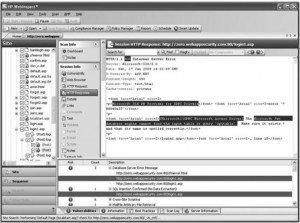 WebInspect testing all kinds of vulnerabilities including XSS vulnerabilities ( Cross Site Scripting), remote and local file inclusion, Operating System command injection, SQL Injection, and etc. It systematically analyze all parameters sent to the application. With this software, you can also simulate an user authentication or any other process using macro. WebInspect provides four authentication mechanisms : Basic, NTLM, Kerberos, and Digest. WebInspect can parse from JavaScript, Flash Content, even capable of testing Web 2.0 Technologies. WebInspect featuring a tool called SQL Injector which you can use to test SQL Injection exploit. it has option of retrieving data from remote server database and showing it to the user in GUI format.
WebInspect testing all kinds of vulnerabilities including XSS vulnerabilities ( Cross Site Scripting), remote and local file inclusion, Operating System command injection, SQL Injection, and etc. It systematically analyze all parameters sent to the application. With this software, you can also simulate an user authentication or any other process using macro. WebInspect provides four authentication mechanisms : Basic, NTLM, Kerberos, and Digest. WebInspect can parse from JavaScript, Flash Content, even capable of testing Web 2.0 Technologies. WebInspect featuring a tool called SQL Injector which you can use to test SQL Injection exploit. it has option of retrieving data from remote server database and showing it to the user in GUI format.
WebInspect Spesification
- Supported Operating System : Microsoft Windows XP Professional SP3, Windows Server 2003 SP2, Windows Vista SP2, Windows 7, Windows 8, and Windows Server 2008 R2
- Requirements : Microsoft SQL Server or Microsoft SQL Server Express Edition, Microsoft .Net 3.5 SP1
- URL : www8.hp.com/us/en/software/software-solution.html?compURI=tcm:245-936139
- Price : Variable depends on vendor
Fixing the SQL Injection Vulnerabilities would not be enough to protect your web application. You need to protect it using Runtime Protection.